Last updated on January 11th, 2022 at 11:12 pm
CBSE Class 11 Computer Science Python Sample Paper 2021
Annual Examination (2020-21)
Class-11
Subject: Computer Science
Time allowed: 3:00 hours/ Maximum Marks:70
All questions are compulsory.
1- Name any two application software. (1)
2- Differentiate between compiler and interpreter? (2)
3- What do you understand by RAM and ROM? (1)
4- Convert the Following as Directed. (2)
i) (23)10=()2
ii) (C4)16=()8
5- Verify the following boolean expression using truth table.(2)
A+BC=(A+B)(A+C)
6- Draw the logic circuit from the following boolean expression.(2)
AB+A’C
7- What do you mean by keyword in python?(1)
8- What is the purpose of ‘else’ in a loop? (1)
9- What is the difference between break and continue statements?(2)
10- Write logical expression for the following?(2)
i) Mark is greater than or equal to 100 but less than 70
ii) City is either ‘Kolkata’ or ‘Mumbai’.
11- Find the output for the following:(2)
x=3
if x>2 or x<5 and x==6;
print (“OK”)
else:
print (“NO Output”)
12- Find the output for the following:(2)
x=20
x=x+5
x=x-10
print (x)
x, y=x-1,50
print (x, y)
13- Find the output for the following:(2)
x, y =2, 6
x, y =y, x+2
print(x, y)
14- The following code is not giving desired output. We want to input value as 20 and obtain output as 40.Identifiy the problem and do the required correction in the code: (2)
x =input (“Enter number :”)
y = x*5
print (y)
15- Find syntax error(s), if any, in the following code: (2)
MAX=’4’
a=int(input”Enter the value of a:”)
b= int(input”Enter the value of b:”)
if(a>b)
MAX=5
for x in range(0, MY_MESSAGE):
print(“%d” %(x))
16- Define operators in python. Explain about relational and logical operators with example.(2)
17- Write a program to enter the side of a square and print its area.(3)
18- Write a program to accept a number from the user and print the table of that number.(3)
19-Convert the following while loop into for loop:(3)
X=5
While (x<10):
print (x+10)
x+=2
20- Identify the valid and invalid identifiers in the following list. (2)
i) x_y125z
ii) _abc@5
iii) abc_d53
iv) break
21- What is flow chart? Draw a flow chart of to calculate sum to two numbers.(2)
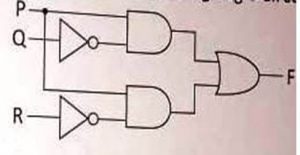
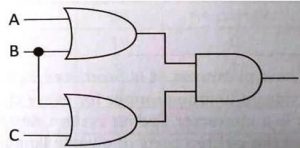
22- Write the equivalent Boolean expression for the following logic circuits. (4)
i)
 ii)
ii)
23- Define the following terms- (4)
i) Tuple
ii) Degree
iii) field
iv) primary key
24- Answer the question based on the table given below:
TABLE: Student
| Column Name | Data Type | Size |
| Roll_No | INTEGER | 4 |
| Name | CHAR | 20 |
| Stipend | CHAR | 7 |
| Stream | CHAR | 15 |
| Grade | CHAR | 1 |
i) Write the SQL command to create the above table.(1)
ii) Insert one record with relevant information, in the table student.(1)
iii) Display all the records of the table Student.(1)
iv) Delete the Student Whose Roll no is 100.(1)
v) Change the Stream of Student to ‘Computer’ Whose Roll no. is 536.(1)
vi) Add one column email of data type CHAR and size 30 to the table student.(1)
25- Answer the question based on the table given below:
TABLE: HOSPITAL
| No. | Name | Age | Department | DateoFadm | Charges | Sex |
| 1 | Arpit | 62 | Surgery | 21/01/98 | 300 | M |
| 2 | Zareena | 22 | ENT | 12/12/97 | 250 | F |
| 3 | Kareem | 32 | Orthopedic | 19/02/98 | 200 | M |
| 4 | Arun | 12 | Surgery | 11/01/98 | 300 | M |
| 5 | Zubin | 30 | ENT | 12/01/98 | 250 | M |
| 6 | Ketaki | 16 | ENT | 24/02/98 | 250 | F |
| 7 | Ankita | 29 | Cardiology | 20/02/98 | 800 | F |
| 8 | Zareen | 45 | Gynecology | 22/02/98 | 300 | F |
| 9 | Kush | 19 | Cardiology | 13/01/98 | 800 | M |
| 10 | Shilpa | 23 | Nuclear Medicine | 21/02/98 | 400 | F |
i) To list the names all the patients admitted after 15/01/98.(1)
ii) To list the names of female patients who are in ENT department.(1)
iii) To list names of all patients with their date of admission in ascending order.(1)
iv) To display Patient’s Name, Charges, Age for only female patients.(1)
v) Find Out the Output of Following SQL Command:- (1)
a) Select COUNT(DISTINCT charges) from HOSPITAL;
b) Select MIN(Age) from HOSPITAL where Sex=”F”;
26- What are the rules for using social networking sites?(2)
27- What is hacking? Suggest any two ways to protect the computer from cyber attack.(2)
28- Define eavesdropping and phishing.(2)
29- What is cyber trolling? How it is done.(2)
30- What are the tips to safely browse the internet?(2)